Hello People,
I know I know, it’s been a while, but who’s counting!
So, a very quick overview of Windows privilege escalation using misconfigured services: If a service’s executable DACLs allows any normal user (non-admin) to delete it, that means that any user can replace that executable with another one of his choosing, thus running any software as Admin! (Please ignore the plethora of “Any”…)
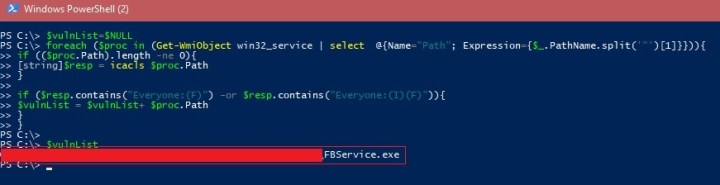
Below is a mini/mildly-dirty script that I wrote to check all local services for any vulnerable services:
$vulnList=$NULL
foreach ($proc in (Get-WmiObject win32_service | select @{Name="Path"; Expression={$_.PathName.split('"')[1]}})){
if (($proc.Path).length -ne 0){
[string]$resp = icacls $proc.Path
}
if ($resp.contains("Everyone:(F)") -or $resp.contains("Everyone:(I)(F)")){
$vulnList = $vulnList+ $proc.Path
}
}
$vulnList
This script will enumerate all the local services paths and check the DACLs of each one, searching for the following ACE: Everyone (F), which means “Everyone” has full control over this file.
While testing on a dummy machine, I found a sneaky service that comes by default with this specific computer model:
To verify that this service runs with Admin Privileges, we quickly check Task Manager:
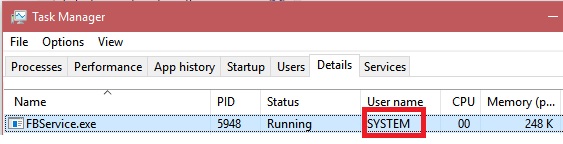
*overjoyed-while-weeping* (That is one super hard-to-find emoji!)
So if I am a malicious user, whether this machine belongs to me or I got a shell somehow, I would simply delete this file, replace it with, for example, a program that adds my user to the local Administrators group, then reboot!
Next step, is to deploy this script to all your machines and collect the output centrally.
This can be done using any Configuration Management tool, for example, using SCCM’s “Run script” feature, or even better, creating a new Configuration Baseline that runs the script on a daily basis, and sends you an Email if any vulnerable services were found!
Below is the script with the Send Mail functionality:
$vulnList = $NULL
foreach ($proc in (Get-WmiObject win32_service | select @{Name="Path"; Expression={$_.PathName.split('"')[1]}})){
if (($proc.Path).length -ne 0){
[string]$resp = icacls $proc.Path
if ($resp.contains("Everyone:(F)") -or $resp.contains("Everyone:(I)(F)")){
$vulnList = $vulnList + $proc.Path
}
}
}
if ($vulnList -ne $NULL){
$From = "noreply@yourcompany.com"
$To = "bearOnBike@yourcompany.com"
$Subject = "Vulnerable services found on "+$env:computername+"!"
$Body = "Dear Admin, The following services can be exploited to gain full administrative privileges over"+ $env:computername +":"+$vulnList
$SMTPServer = "notVerySecureSMTP.yourcompany.com"
$SMTPPort = "25"
Send-MailMessage -From $From -to $To -Subject $Subject -Body $Body -SmtpServer $SMTPServer -port $SMTPPort -BodyAsHtml
}
Of course, don’t forget to add some HTML Break Line tags to properly format the sent Email message.
That’s it, you can go back to your Fortnite-ing.