There are tons of remote support tools for AD environments, but most of them are commercial, and some of them are user initiated (like Lync 2010+ desktop sharing feature), today we will implement an agentless (sort of), free and pretty effective solution, the end result is a box that you enter the destined Username in (the person you’re trying to help), et voila, you have control over his screen ! (gentlemen, after his permission, of course)
Chapter I :
The base application that we will use is “Windows Remote Assistance” which ships for free with most Windows 7 flavors, the rest is scripting gimmicks.
Out of the box, Windows remote assistance will work if the requester sent an invitation file to the helper, but in our case, we want to initiate the process by offering our help before we even hear the nagging.
To do so, we need to create and link a GPO to our computers OU that enables just that :
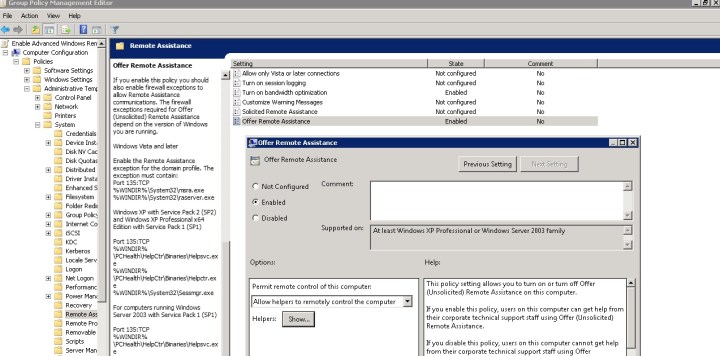
Computer Configuration > Policies > Administrative Templates > System > Remote Assistance
Enable the “Offer Remote Assistance” option and select who can offer remote support, typically you will add your Help Desk group
After you gpupdate the end-user’s machine, try it:
Open “Windows Remote Assistance” from your helper workstation, then click on Continue reading